Modern operating systems support the IKEv2 standard. Internet Key Exchange (IKE or IKEv2) is the protocol used to set up a Security Association (SA) in the IPsec protocol suite. Compared to IKE version 1, IKEv2 contains improvements such as Standard Mobility support through MOBIKE, and improved reliability.
Libreswan can authenticate IKEv2 clients on the basis of X.509 Machine Certificates using RSA signatures. This method does not require an IPsec PSK, username or password. It can be used with Windows, macOS, iOS, Android, Chrome OS, Linux and RouterOS.
¶ Create IKEv2 VPN for cloud context access
Once connected to the VPN, you will have access to all devices on the 26.0.0.0/8 address range.
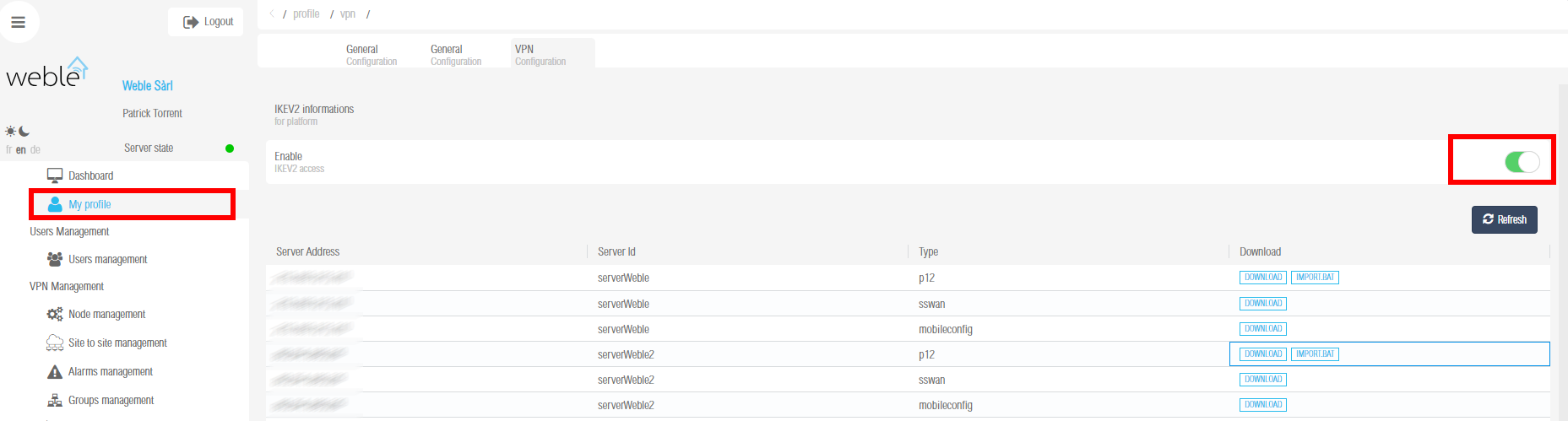
- My Profile
- VPN Configuration
- Enable ikev2 connection
- Download your IKEv2 Configuration depending your platform.
¶ Create IKEv2 Connection for a remote network access
Once connected to the VPN, you will have access to the entire remote network connected to the device.
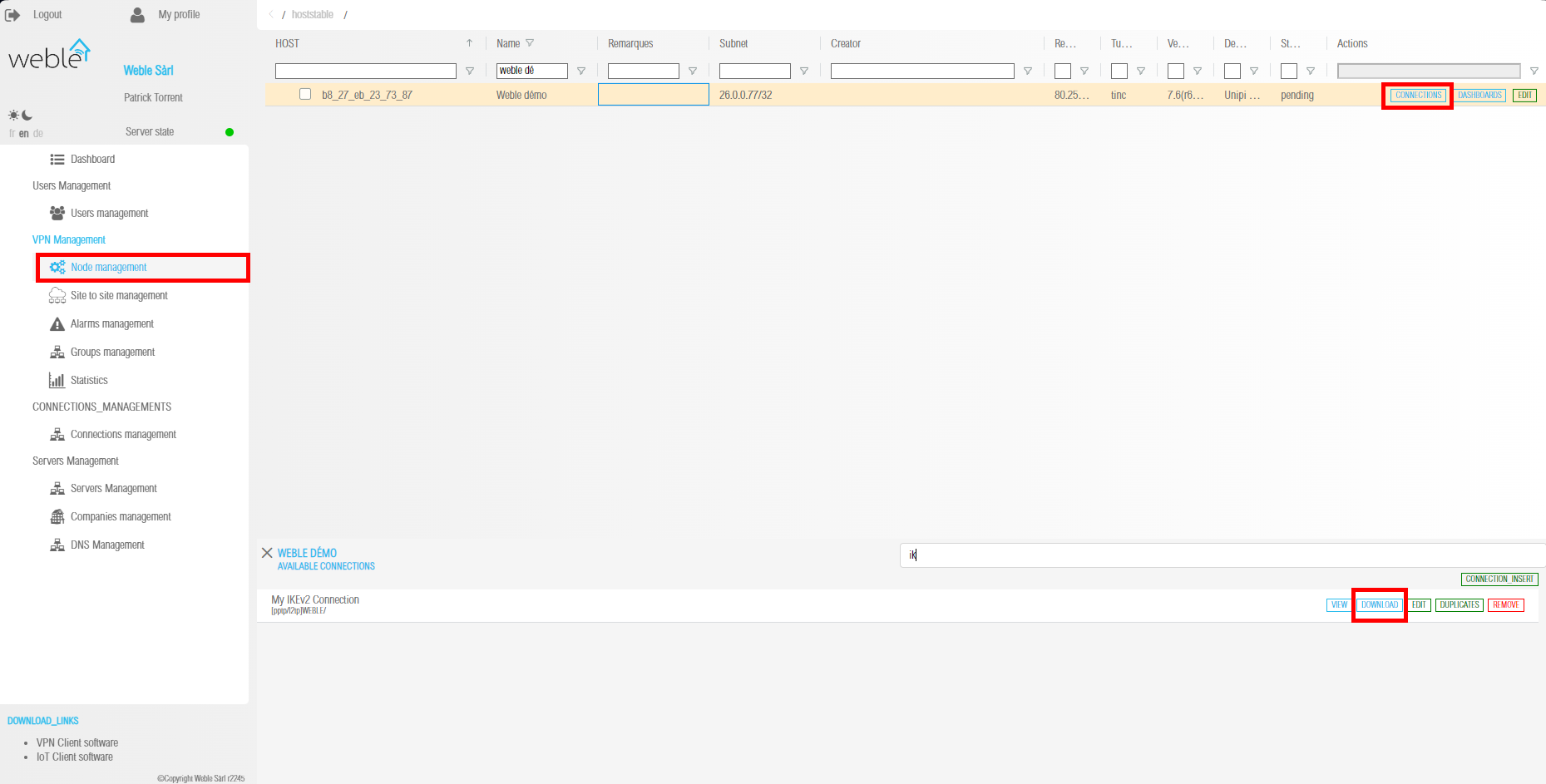
- Node management
- Select the host your want to add an IKEv2 VPN Connection
- Insert connnection
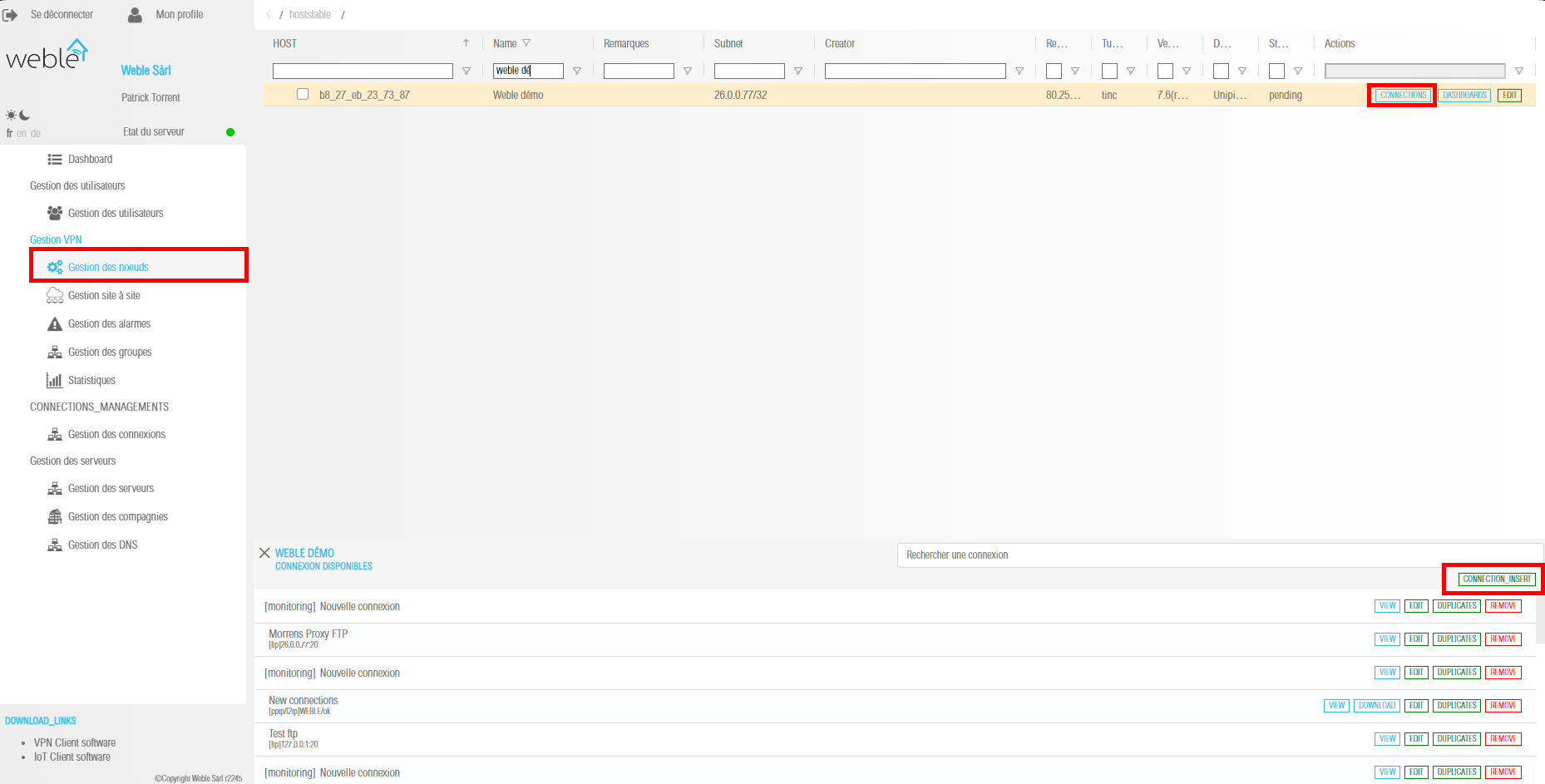
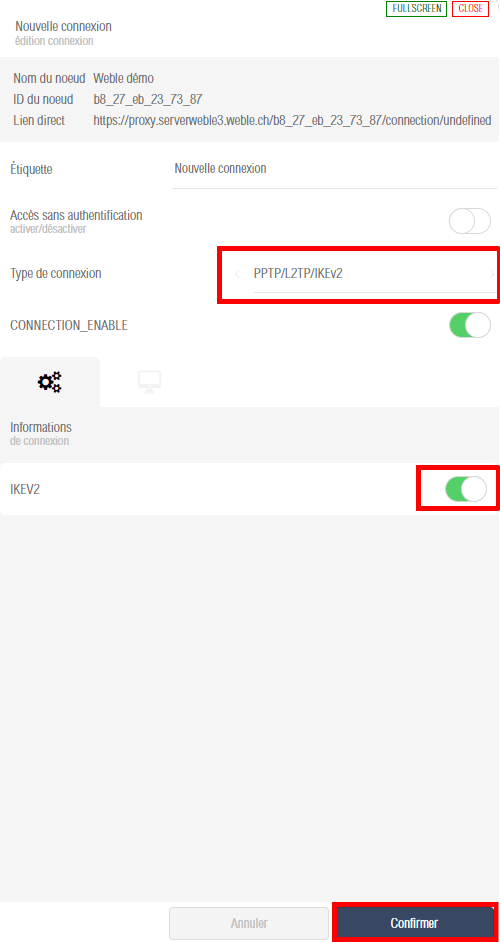
- Set a name to your connection
- Enable it
- Select PPTP/l2TP/IKEv2 Connection type
- Select IKEv2
- Press save
 !
!
¶ Download IKEv2 configuration
¶ Session Connection
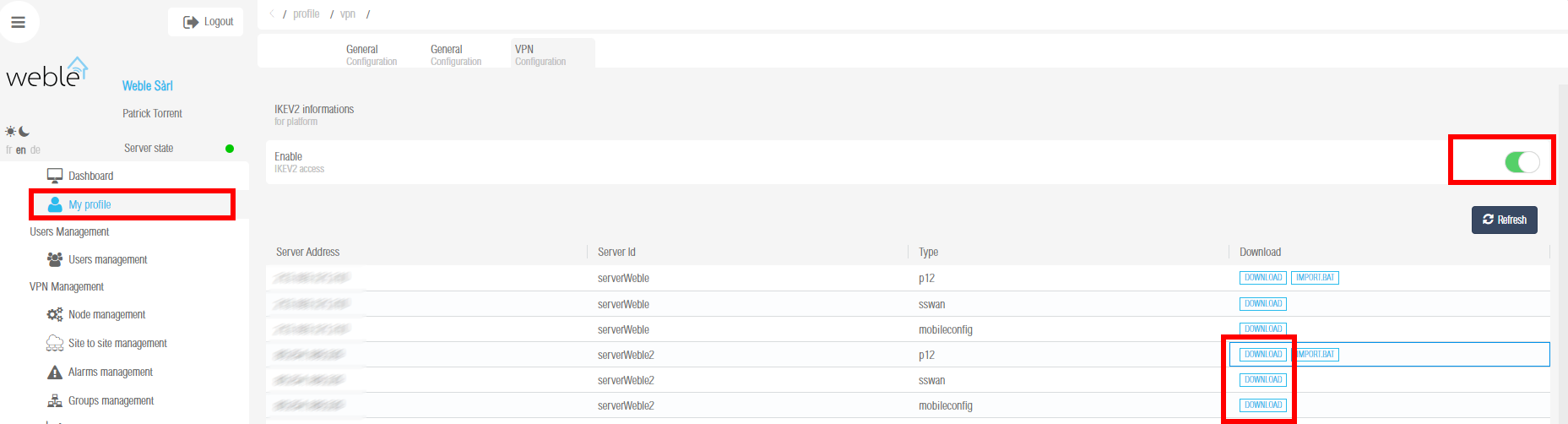
- My Profile
- VPN Configuration
- Select the server you want to connect
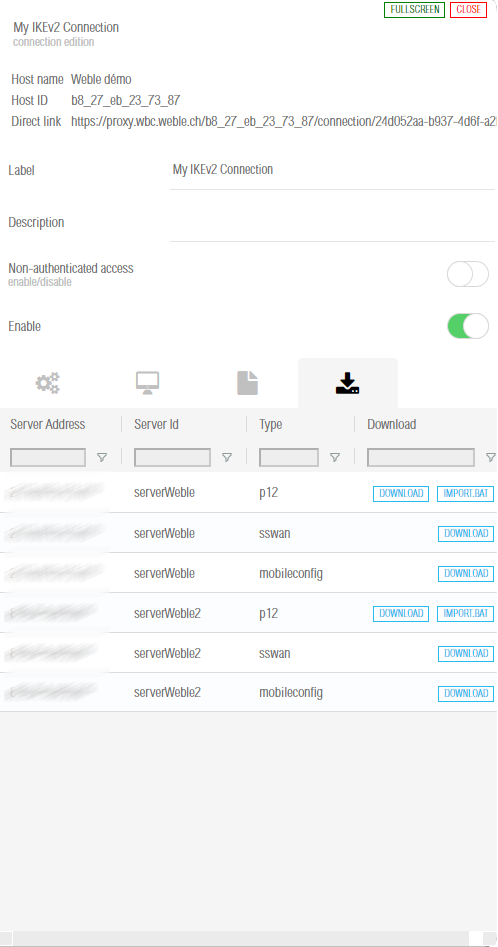
- Select the type of certificate you want to download
¶ Host Connection
- Node management
- Select the host your want to download IKEv2 VPN Connection
- Find your Host Connection
- Click on download
¶ Dashboard Connection
- Node management
- Select the host your want to download IKEv2 VPN Dashboard Connection
- Find your Dashboard Connection
- Click on download
¶ Configure IKEv2 VPN clients
¶ Windows 7, 8, 10 and 11
¶ Auto-import configuration
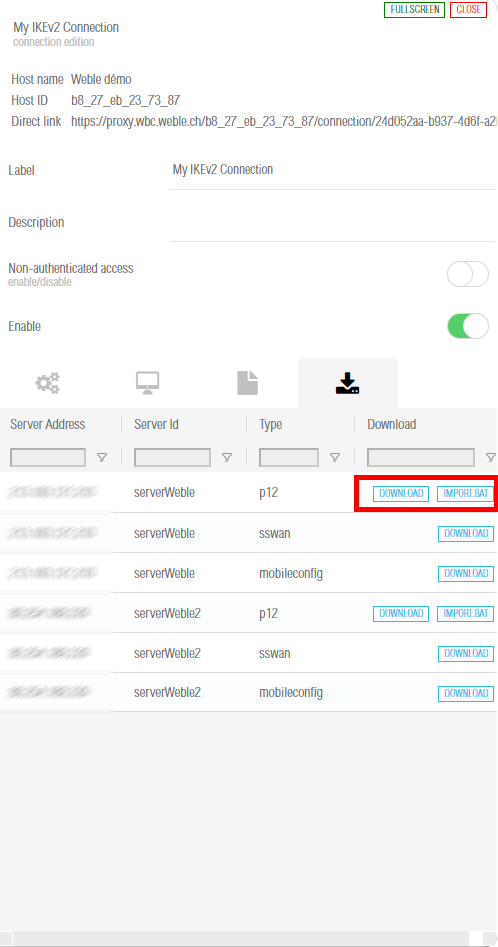
Windows 8, 10 and 11 users can automatically import IKEv2 configuration:
- Go the the download section of your dashboard connection or host connection
- Securely download the generated
IMPORT.batfile to your computer by pressingIMPORT.batbutton. - Unzip the downloaded zip file
- Right-click on the saved script (.bat), select Run as administrator and follow the prompts.
- You can skip all questions by pressing enter
- You connection will be automatically inserted
¶ Manually import configuration
Alternatively, Windows 7, 8, 10 and 11 users can manually import IKEv2 configuration:
- Go the the download section of your dashboard connection or host connection
- Securely download the generated
.p12file to your computer by pressing "DOWNLOAD" button, then import it into the certificate store.
To import the.p12file, run the following from an elevated command prompt:
# Import .p12 file (replace with your own value)
certutil -f -importpfx "\path\to\your\file.p12" NoExport
Note: If there is no password for client config files, press Enter to continue, or if manually importing the
.p12file, leave the password field blank.
Alternatively, you can manually import the .p12 file. Make sure that the client cert is placed in "Personal -> Certificates", and the CA cert is placed in "Trusted Root Certification Authorities -> Certificates".
-
On the Windows computer, add a new IKEv2 VPN connection.
For Windows 8, 10 and 11, it is recommended to create the VPN connection using the following commands from a command prompt, for improved security and performance.
# Create VPN connection (replace server address with your own value)
powershell -command ^"Add-VpnConnection -ServerAddress 'Your VPN Server IP (or DNS name)' ^
-Name 'My IKEv2 VPN' -TunnelType IKEv2 -AuthenticationMethod MachineCertificate ^
-EncryptionLevel Required -PassThru^"
# Set IPsec configuration
powershell -command ^"Set-VpnConnectionIPsecConfiguration -ConnectionName 'My IKEv2 VPN' ^
-AuthenticationTransformConstants GCMAES128 -CipherTransformConstants GCMAES128 ^
-EncryptionMethod AES256 -IntegrityCheckMethod SHA256 -PfsGroup None ^
-DHGroup Group14 -PassThru -Force^"
Windows 7 does not support these commands, you can manually create the VPN connection.
Note: The server address you specify must exactly match the server address in the output of the IKEv2 helper script. For example, if you specified the server's DNS name during IKEv2 setup, you must enter the DNS name in the Internet address field.
-
This step is required if you manually created the VPN connection.
Enable stronger ciphers for IKEv2 with a one-time registry change. Download and import the
.regfile below, or run the following from an elevated command prompt. Read more here.-
For Windows 7, 8, 10 and 11 (download .reg file)
REG ADD HKLM\SYSTEM\CurrentControlSet\Services\RasMan\Parameters /v NegotiateDH2048_AES256 /t REG_DWORD /d 0x1 /f
-
To connect to the VPN: Click on the wireless/network icon in your system tray, select the new VPN entry, and click Connect. Once connected, you can verify that your traffic is being routed properly by looking up your IP address on Google. It should say "Your public IP address is Your VPN Server IP".
If you get an error when trying to connect, see Troubleshooting.
Remove the IKEv2 VPN connection.
Using the following steps, you can remove the VPN connection and optionally restore the computer to the status before IKEv2 configuration import.
-
Remove the added VPN connection in Windows Settings - Network - VPN. Windows 7 users can remove the VPN connection in Network and Sharing Center - Change adapter settings.
-
(Optional) Remove IKEv2 certificates.
-
Press Win+R, or search for
mmcin the Start Menu. Open Microsoft Management Console. -
Open
File - Add/Remove Snap-In. Select to addCertificatesand in the window that opens, selectComputer account -> Local Computer. Click onFinish -> OKto save the settings. -
Go to
Certificates - Personal - Certificatesand delete the IKEv2 client certificate. The name of the certificate is the same as the IKEv2 client name you specified (default:vpnclient). The certificate was issued byIKEv2 VPN CA. -
Go to
Certificates - Trusted Root Certification Authorities - Certificatesand delete the IKEv2 VPN CA certificate. The certificate was issued toIKEv2 VPN CAbyIKEv2 VPN CA. Before deleting, make sure that there are no other certificate(s) issued byIKEv2 VPN CAinCertificates - Personal - Certificates.
-
-
(Optional. For users who manually created the VPN connection) Restore registry settings. Note that you should backup the registry before editing.
-
Press Win+R, or search for
regeditin the Start Menu. Open Registry Editor. -
Go to
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Rasman\Parametersand delete the item with nameNegotiateDH2048_AES256, if it exists.
-
¶ MAC
¶ OS X (macOS)
First, securely transfer the generated .mobileconfig file to your Mac, then double-click and follow the prompts to import as a macOS profile. If your Mac runs macOS Big Sur or newer, open System Preferences and go to the Profiles section to finish importing. For macOS Ventura and newer, open System Settings and search for Profiles. When finished, check to make sure "IKEv2 VPN" is listed under System Preferences -> Profiles.
To connect to the VPN:
- Open System Preferences and go to the Network section.
- Select the VPN connection with
Your VPN Server IP(or DNS name). - Check the Show VPN status in menu bar checkbox. For macOS Ventura and newer, this setting can be configured in System Settings -> Control Center -> Menu Bar Only section.
- Click Connect, or slide the VPN switch ON.
(Optional feature) Enable VPN On Demand to automatically start a VPN connection when your Mac is on Wi-Fi. To enable, check the Connect on demand checkbox for the VPN connection, and click Apply. To find this setting on macOS Ventura and newer, click on the "i" icon on the right of the VPN connection.
You can customize VPN On Demand rules to exclude certain Wi-Fi network(s) such as your home network. See "Guide: Customize IKEv2 VPN On Demand rules for macOS and iOS" in Book: Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server.
If you manually set up IKEv2 without using the helper script, click here for instructions.
First, securely transfer the generated .p12 file to your Mac, then double-click to import into the login keychain in Keychain Access. Next, double-click on the imported IKEv2 VPN CA certificate, expand Trust and select Always Trust from the IP Security (IPsec) drop-down menu. Close the dialog using the red "X" on the top-left corner. When prompted, use Touch ID or enter your password and click "Update Settings".
When finished, check to make sure both the new client certificate and IKEv2 VPN CA are listed under the Certificates category of login keychain.
- Open System Preferences and go to the Network section.
- Click the + button in the lower-left corner of the window.
- Select VPN from the Interface drop-down menu.
- Select IKEv2 from the VPN Type drop-down menu.
- Enter anything you like for the Service Name.
- Click Create.
- Enter
Your VPN Server IP(or DNS name) for the Server Address.
Note: If you specified the server's DNS name (instead of its IP address) during IKEv2 setup, you must enter the DNS name in the Server Address and Remote ID fields. - Enter
Your VPN Server IP(or DNS name) for the Remote ID. - Enter
Your VPN client namein the Local ID field.
Note: This must match exactly the client name you specified during IKEv2 setup. Same as the first part of your.p12filename. - Click the Authentication Settings... button.
- Select None from the Authentication Settings drop-down menu.
- Select the Certificate radio button, then select the new client certificate.
- Click OK.
- Check the Show VPN status in menu bar checkbox.
- Click Apply to save the VPN connection information.
- Click Connect.
Once connected, you can verify that your traffic is being routed properly by looking up your IP address on Google. It should say "Your public IP address is Your VPN Server IP".
If you get an error when trying to connect, see Troubleshooting.
macOS 14 (Sonoma) has a minor issue that may cause IKEv2 VPN to disconnect and reconnect once every 24-48 minutes. Other macOS versions are not affected. For more details and a workaround, see [macOS Sonoma clients reconnect](#macos-sonoma-clients-reconnect
**Remove the IKEv2 VPN connection.**
To remove the IKEv2 VPN connection, open System Preferences -> Profiles and remove the IKEv2 VPN profile you added.¶ iOS
First, securely transfer the generated .mobileconfig file to your iOS device, then import it as an iOS profile. To transfer the file, you may use:
- AirDrop, or
- Upload to your device (any App folder) using File Sharing, then open the "Files" App on your iOS device, move the uploaded file to the "On My iPhone" folder. After that, tap the file and go to the "Settings" App to import, or
- Host the file on a secure website of yours, then download and import it in Mobile Safari.
Or you can download it directly from the cloud
When finished, check to make sure "IKEv2 VPN" is listed under Settings -> General -> VPN & Device Management or Profile(s).
To connect to the VPN:
- Go to Settings -> VPN. Select the VPN connection with
Your VPN Server IP(or DNS name). - Slide the VPN switch ON.
(Optional feature) Enable VPN On Demand to automatically start a VPN connection when your iOS device is on Wi-Fi. To enable, tap the "i" icon on the right of the VPN connection, and enable Connect On Demand.
You can customize VPN On Demand rules to exclude certain Wi-Fi network(s) such as your home network, or to start the VPN connection both on Wi-Fi and cellular. See "Guide: Customize IKEv2 VPN On Demand rules for macOS and iOS" in Book: Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server.
If you manually set up IKEv2 without using the helper script, click here for instructions.
First, securely transfer the generated ca.cer and .p12 files to your iOS device, then import them one by one as iOS profiles. To transfer the files, you may use:
- AirDrop, or
- Upload to your device (any App folder) using File Sharing, then open the "Files" App on your iOS device, move the uploaded files to the "On My iPhone" folder. After that, tap each file and go to the "Settings" App to import, or
- Host the files on a secure website of yours, then download and import them in Mobile Safari.
When finished, check to make sure both the new client certificate and IKEv2 VPN CA are listed under Settings -> General -> VPN & Device Management or Profile(s).
- Go to Settings -> General -> VPN & Device Management -> VPN.
- Tap Add VPN Configuration....
- Tap Type. Select IKEv2 and go back.
- Tap Description and enter anything you like.
- Tap Server and enter
Your VPN Server IP(or DNS name).
Note: If you specified the server's DNS name (instead of its IP address) during IKEv2 setup, you must enter the DNS name in the Server and Remote ID fields. - Tap Remote ID and enter
Your VPN Server IP(or DNS name). - Enter
Your VPN client namein the Local ID field.
Note: This must match exactly the client name you specified during IKEv2 setup. Same as the first part of your.p12filename. - Tap User Authentication. Select None and go back.
- Make sure the Use Certificate switch is ON.
- Tap Certificate. Select the new client certificate and go back.
- Tap Done.
- Slide the VPN switch ON.
Remove the IKEv2 VPN connection.
To remove the IKEv2 VPN connection, open Settings -> General -> VPN & Device Management or Profile(s) and remove the IKEv2 VPN profile you added.
¶ Android
¶ Using strongSwan VPN client
Android users can connect using strongSwan VPN client.
- Securely transfer the generated
.sswanfile to your Android device. - Install strongSwan VPN Client from Google Play, F-Droid or strongSwan download server.
- Launch the strongSwan VPN client.
- Tap the "more options" menu on top right, then tap Import VPN profile.
- Choose the
.sswanfile you transferred from the VPN server.
Note: To find the.sswanfile, tap the three-line menu button, then browse to the location you saved the file. - On the "Import VPN profile" screen, tap IMPORT CERTIFICATE FROM VPN PROFILE, and follow the prompts.
- On the "Choose certificate" screen, select the new client certificate, then tap Select.
- Tap IMPORT.
- Tap the new VPN profile to connect.
(Optional feature) You can choose to enable the "Always-on VPN" feature on Android. Launch the Settings app, go to Network & internet -> Advanced -> VPN, click the gear icon on the right of "strongSwan VPN Client", then enable the Always-on VPN and Block connections without VPN options.
¶ Android 10 and newer
- Securely transfer the generated
.p12file to your Android device. - Install strongSwan VPN Client from Google Play, F-Droid or strongSwan download server.
- Launch the Settings application.
- Go to Security -> Advanced -> Encryption & credentials.
- Tap Install a certificate.
- Tap VPN & app user certificate.
- Choose the
.p12file you transferred from the VPN server, and follow the prompts.
Note: To find the.p12file, tap the three-line menu button, then browse to the location you saved the file. - Launch the strongSwan VPN client and tap Add VPN Profile.
- Enter
Your VPN Server IP(or DNS name) in the Server field.
Note: If you specified the server's DNS name (instead of its IP address) during IKEv2 setup, you must enter the DNS name in the Server field. - Select IKEv2 Certificate from the VPN Type drop-down menu.
- Tap Select user certificate, select the new client certificate and confirm.
- (Important) Tap Show advanced settings. Scroll down, find and enable the Use RSA/PSS signatures option.
- Save the new VPN connection, then tap to connect.
¶ Android 4 to 9
- Securely transfer the generated
.p12file to your Android device. - Install strongSwan VPN Client from Google Play, F-Droid or strongSwan download server.
- Launch the strongSwan VPN client and tap Add VPN Profile.
- Enter
Your VPN Server IP(or DNS name) in the Server field.
Note: If you specified the server's DNS name (instead of its IP address) during IKEv2 setup, you must enter the DNS name in the Server field. - Select IKEv2 Certificate from the VPN Type drop-down menu.
- Tap Select user certificate, then tap Install certificate.
- Choose the
.p12file you transferred from the VPN server, and follow the prompts.
Note: To find the.p12file, tap the three-line menu button, then browse to the location you saved the file. - (Important) Tap Show advanced settings. Scroll down, find and enable the Use RSA/PSS signatures option.
- Save the new VPN connection, then tap to connect.
¶ Android 11+ (recommended)
Android 11+ users can also connect using the native IKEv2 client.
- Securely transfer the generated
.p12file to your Android device. - Launch the Settings application.
- Go to Security -> Advanced -> Encryption & credentials.
- Tap Install a certificate.
- Tap VPN & app user certificate.
- Choose the
.p12file you transferred from the VPN server.
Note: To find the.p12file, tap the three-line menu button, then browse to the location you saved the file. - Enter a name for the certificate, then tap OK.
- Go to Settings -> Network & internet -> VPN, then tap the "+" button.
- Enter a name for the VPN profile.
- Select IKEv2/IPSec RSA from the Type drop-down menu.
- Enter
Your VPN Server IP(or DNS name) in the Server address field.
Note: This must exactly match the server address in the output of the IKEv2 helper script. - Enter anything (e.g.
empty) in the IPSec identifier field.
Note: This field should not be required. It is a bug in Android. - Select the certificate you imported from the IPSec user certificate drop-down menu.
- Select the certificate you imported from the IPSec CA certificate drop-down menu.
- Select (receive from server) from the IPSec server certificate drop-down menu.
- Tap Save. Then tap the new VPN connection and tap Connect.
¶ Chrome OS
First, on your VPN server, export the CA certificate as ca.cer:
sudo certutil -L -d sql:/etc/ipsec.d -n "IKEv2 VPN CA" -a -o ca.cer
Securely transfer the generated .p12 and ca.cer files to your Chrome OS device.
Install user and CA certificates:
- Open a new tab in Google Chrome.
- In the address bar, enter chrome://settings/certificates
- (Important) Click Import and Bind, not Import.
- In the box that opens, choose the
.p12file you transferred from the VPN server and select Open. - Click OK if the certificate does not have a password. Otherwise, enter the certificate's password.
- Click the Authorities tab. Then click Import.
- In the box that opens, select All files in the drop-down menu at the bottom left.
- Choose the
ca.cerfile you transferred from the VPN server and select Open. - Keep the default options and click OK.
Add a new VPN connection:
- Go to Settings -> Network.
- Click Add connection, then click Add built-in VPN.
- Enter anything you like for the Service name.
- Select IPsec (IKEv2) in the Provider type drop-down menu.
- Enter
Your VPN Server IP(or DNS name) for the Server hostname. - Select User certificate in the Authentication type drop-down menu.
- Select IKEv2 VPN CA [IKEv2 VPN CA] in the Server CA certificate drop-down menu.
- Select IKEv2 VPN CA [client name] in the User certificate drop-down menu.
- Leave other fields blank.
- Enable Save identity and password.
- Click Connect.
(Optional feature) You can choose to enable the "Always-on VPN" feature on Chrome OS. To manage this setting, go to Settings -> Network, then click VPN.
¶ Linux
Before configuring Linux VPN clients, you must make the following change on the VPN server: Edit /etc/ipsec.d/ikev2.conf on the server. Append authby=rsa-sha1 to the end of the conn ikev2-cp section, indented by two spaces. Save the file and run service ipsec restart.
To configure your Linux computer to connect to IKEv2 as a VPN client, first install the strongSwan plugin for NetworkManager:
# Ubuntu and Debian
sudo apt-get update
sudo apt-get install network-manager-strongswan
# Arch Linux
sudo pacman -Syu # upgrade all packages
sudo pacman -S networkmanager-strongswan
# Fedora
sudo yum install NetworkManager-strongswan-gnome
# CentOS
sudo yum install epel-release
sudo yum --enablerepo=epel install NetworkManager-strongswan-gnome
Next, securely transfer the generated .p12 file from the VPN server to your Linux computer. After that, extract the CA certificate, client certificate and private key. Replace vpnclient.p12 in the example below with the name of your .p12 file.
# Example: Extract CA certificate, client certificate and private key.
# You may delete the .p12 file when finished.
# Note: You may need to enter the import password, which can be found
# in the output of the IKEv2 helper script. If the output does not
# contain an import password, press Enter to continue.
# Note: If using OpenSSL 3.x (run "openssl version" to check),
# append "-legacy" to the 3 commands below.
openssl pkcs12 -in vpnclient.p12 -cacerts -nokeys -out ca.cer
openssl pkcs12 -in vpnclient.p12 -clcerts -nokeys -out client.cer
openssl pkcs12 -in vpnclient.p12 -nocerts -nodes -out client.key
rm vpnclient.p12
# (Important) Protect certificate and private key files
# Note: This step is optional, but strongly recommended.
sudo chown root:root ca.cer client.cer client.key
sudo chmod 600 ca.cer client.cer client.key
You can then set up and enable the VPN connection:
- Go to Settings -> Network -> VPN. Click the + button.
- Select IPsec/IKEv2 (strongswan).
- Enter anything you like in the Name field.
- In the Gateway (Server) section, enter
Your VPN Server IP(or DNS name) for the Address. - Select the
ca.cerfile for the Certificate. - In the Client section, select Certificate(/private key) in the Authentication drop-down menu.
- Select Certificate/private key in the Certificate drop-down menu (if exists).
- Select the
client.cerfile for the Certificate (file). - Select the
client.keyfile for the Private key. - In the Options section, check the Request an inner IP address checkbox.
- In the Cipher proposals (Algorithms) section, check the Enable custom proposals checkbox.
- Leave the IKE field blank.
- Enter
aes128gcm16in the ESP field. - Click Add to save the VPN connection information.
- Turn the VPN switch ON.
Alternatively, you may connect using the command line. See #1399 and #1007 for example steps. If you encounter error Could not find source connection, edit /etc/netplan/01-netcfg.yaml and replace renderer: networkd with renderer: NetworkManager, then run sudo netplan apply. To connect to the VPN, run sudo nmcli c up VPN. To disconnect: sudo nmcli c down VPN.
Once connected, you can verify that your traffic is being routed properly by looking up your IP address on Google. It should say "Your public IP address is Your VPN Server IP".
If you get an error when trying to connect, see Troubleshooting.
¶ RouterOS
Note: These steps were contributed by @Unix-User. It is recommended to run terminal commands via an SSH connection, e.g. via Putty.
-
Securely transfer the generated
.p12file to your computer.Click to see screencast.

-
In WinBox, go to System > certificates > import. Import the
.p12certificate file twice (yes, import the same file two times!). Verify in your certificates panel. You will see 2 files, the one that is marked KT is the key.Click to see screencast.

Or you can use terminal instead (empty passphrase):
[admin@MikroTik] > /certificate/import file-name=mikrotik.p12 passphrase: certificates-imported: 2 private-keys-imported: 0 files-imported: 1 decryption-failures: 0 keys-with-no-certificate: 0 [admin@MikroTik] > /certificate/import file-name=mikrotik.p12 passphrase: certificates-imported: 0 private-keys-imported: 1 files-imported: 1 decryption-failures: 0 keys-with-no-certificate: 0 -
Run these commands in terminal. Replace the following with your own values.
YOUR_VPN_SERVER_IP_OR_DNS_NAMEis your VPN server IP or DNS name.
IMPORTED_CERTIFICATEis the name of the certificate from step 2 above, e.g.vpnclient.p12_0
(the one flagged with KT - Priv. Key Trusted - if not flagged as KT, import certificate again).
THESE_ADDRESSES_GO_THROUGH_VPNare the local network addresses that you want to browse through the VPN.
Assuming that your local network behind RouterOS is192.168.0.0/24, you can use192.168.0.0/24
for the entire network, or use192.168.0.10for just one device, and so on./ip firewall address-list add address=THESE_ADDRESSES_GO_THROUGH_VPN list=local /ip ipsec mode-config add name=ike2-rw responder=no src-address-list=local /ip ipsec policy group add name=ike2-rw /ip ipsec profile add name=ike2-rw /ip ipsec peer add address=YOUR_VPN_SERVER_IP_OR_DNS_NAME exchange-mode=ike2 \ name=ike2-rw-client profile=ike2-rw /ip ipsec proposal add name=ike2-rw pfs-group=none /ip ipsec identity add auth-method=digital-signature certificate=IMPORTED_CERTIFICATE \ generate-policy=port-strict mode-config=ike2-rw \ peer=ike2-rw-client policy-template-group=ike2-rw /ip ipsec policy add group=ike2-rw proposal=ike2-rw template=yes -
For more information, see #1112.
tested on
mar/02/2022 12:52:57 by RouterOS 6.48
RouterBOARD 941-2nD